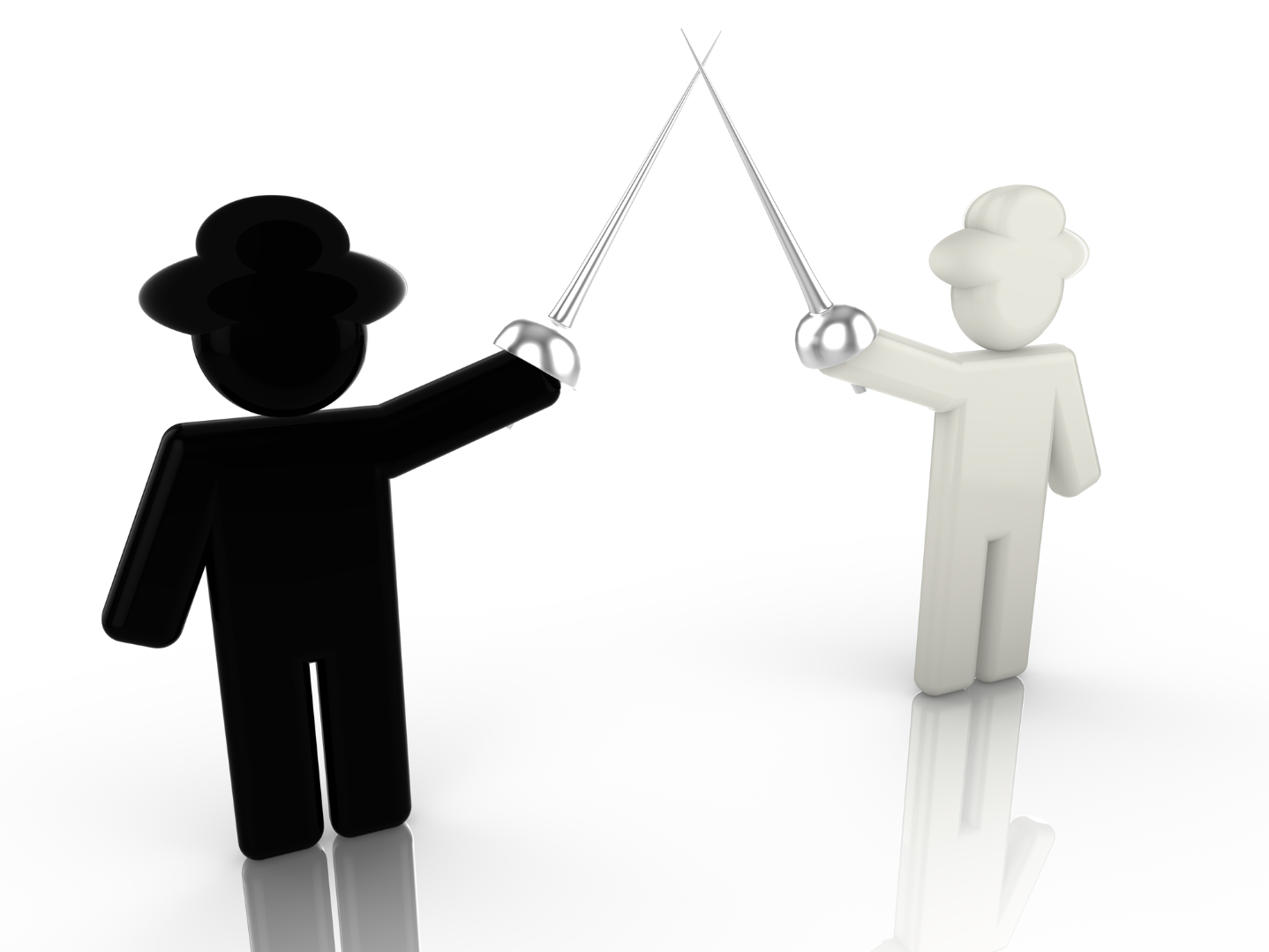
In this blog, I want to talk about white hat and black hat hackers, specifically how they operate and their impact on cybersecurity.
Introduction
Hacking techniques can steal sensitive information, and security measures are constantly evolving to protect networks from cybercriminals. The world of cybersecurity includes both legal and illegal hacking practices. The key players in this field are white hat and black hat hackers. While white hat hackers are ethical and work to improve security, black hat hackers engage in illegal activities to exploit vulnerabilities for malicious purposes.
White Hat Hackers
White hat hackers, also known as ethical hackers, are professionals who use their skills to improve security. They identify weaknesses in computer systems and recommend improvements to prevent attacks. Their main goal is to protect systems by finding vulnerabilities before malicious hackers can exploit them. White hat hackers perform penetration testing, which involves attempting to break into systems to assess their security. By doing so, they help strengthen the system’s defenses against black hat hackers.
The Influence of White Hat Hackers
White hat hackers have a significant impact on the cybersecurity industry. Some notable figures include:
- Tim Berners-Lee: Known for his contributions to computer science, Berners-Lee helped shape the global web we use today.
- Greg Hogloud: An expert in computer forensics, Hogloud has made valuable contributions to malware detection and online gaming security.
Ethical Hacking
Ethical hacking involves testing systems to identify vulnerabilities, but it is done with positive intentions to improve security. It focuses on enhancing data protection and strengthening defenses against unauthorized access. Ethical hacking includes penetration testing, where ethical hackers try to break into systems to find weaknesses before malicious hackers can exploit them.
White Hat Penetration Testing
Penetration testing, often performed by white hat hackers, is essential for identifying vulnerabilities in enterprise networks. These tests help businesses understand their security gaps and provide recommendations to fix them. By proactively testing systems, white hat hackers can help prevent real-world attacks by addressing weaknesses before they become a threat. Penetration testing involves checking for infiltrations, breaking into systems, and ensuring that security measures are robust enough to withstand potential cyberattacks.
White Hat Hacking Tactics
White hat hackers use many of the same tools and techniques as black hat hackers but for ethical purposes. They employ social engineering methods, use advanced tools, and find vulnerabilities in data systems to strengthen security. Their goal is to ensure the safety of data systems by finding weaknesses and addressing them before malicious hackers can take advantage.
Automated White Hat Hackers
Automated white hat hackers use specialized tools to test systems quickly and efficiently. Their primary focus is on infiltrating networks to identify vulnerabilities and ensure security measures are effective. By automating certain tasks, white hat hackers can rapidly assess large-scale networks and implement necessary changes.
Black Hat Hackers
Black hat hackers are malicious individuals who exploit vulnerabilities in systems to steal sensitive information. Their primary goal is to bypass security measures and gain unauthorized access to personal, financial, or corporate data. Black hat hackers often use malware, phishing attacks, and other techniques to breach networks. They can cause significant harm, including identity theft, financial loss, and widespread damage to organizations.
The Dangers of Black Hat Hacking
Black hat hacking is a serious threat, as it can lead to the theft of personal data, financial information, and even the destruction of entire systems. These hackers focus on gaining unauthorized access to networks and causing as much damage as possible. Their activities are illegal and can have far-reaching consequences for individuals and businesses alike.
Hacking as a Business
Black hat hacking has become a business in itself. Many hackers operate within organized criminal networks, selling malware, tools, and hacking services to the highest bidder. These criminal organizations collaborate to spread malicious software and exploit vulnerabilities for financial gain. The scale of black hat hacking is vast, with hackers offering their services to various clients in exchange for money, further contributing to the global cybercrime problem.
The Global Impact of Black Hat Hacking
Black hat hacking is a global issue that affects everyone. The scale of these attacks is enormous, and it’s difficult to prevent every potential threat. Cybersecurity tools, such as antivirus software and firewalls, play an essential role in protecting against black hat hackers, but they are not foolproof. To minimize risk, businesses and individuals must stay vigilant and continuously update their security measures.
By understanding the differences between white hat and black hat hackers, we can appreciate the importance of ethical hacking in maintaining cybersecurity and protecting sensitive information.