Penetration testing, or pen testing, is a simulated cyber-attack on your computer system designed to identify potential vulnerabilities that could be exploited. In the context of web application security, pen testing is often used to improve the security of a web application firewall (WAF).
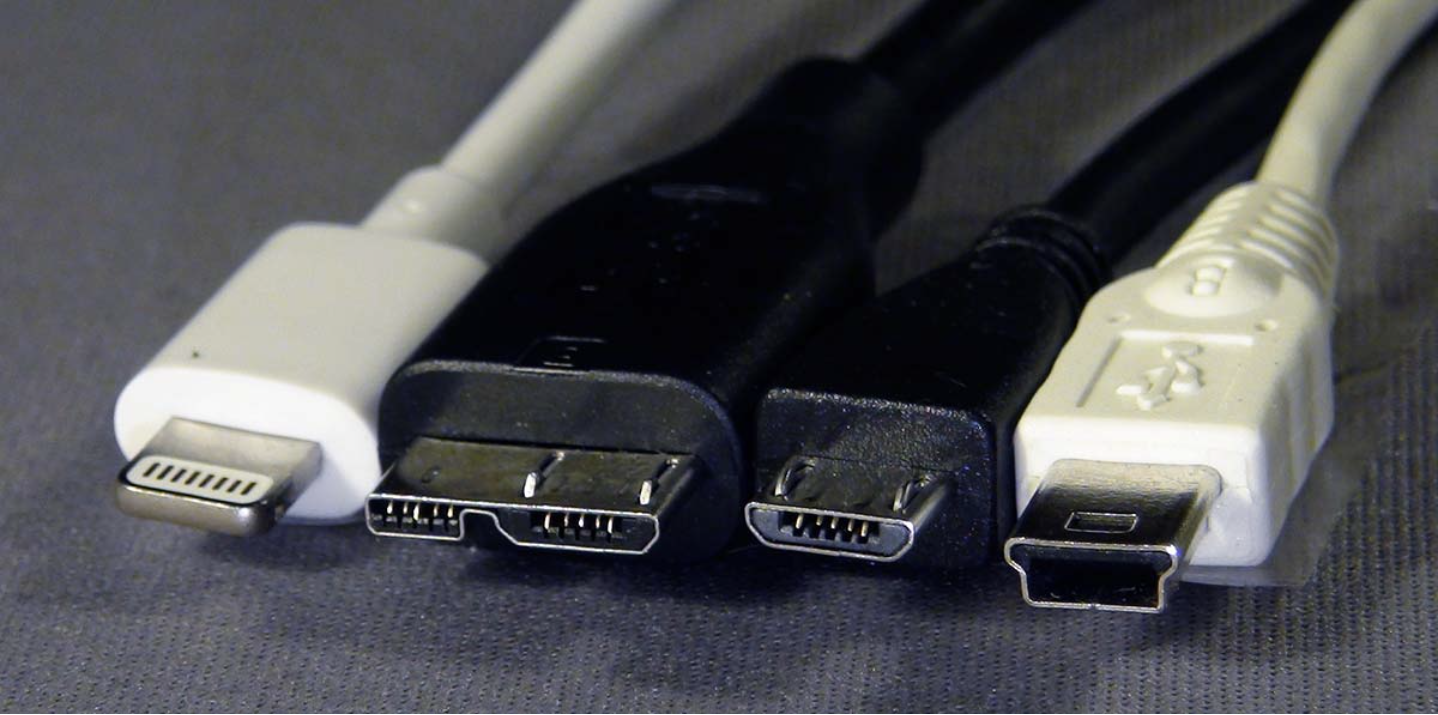
Pen testing involves trying to penetrate various application systems (such as APIs and frontend/backend servers) to uncover weaknesses, like unsanitized inputs that could be susceptible to code injection attacks.
The insights from a penetration test can help refine WAF security policies and fix any vulnerabilities that are discovered.
Penetration Testing Stages
- Planning and Reconnaissance: The first step is defining the scope and objectives of the test, including which systems will be targeted and the methods to be used. This phase also involves gathering intelligence, such as domain names and mail server details, to understand how the target operates and identify potential vulnerabilities.
- Scanning: The next step is testing how the target application responds to various attack attempts. This is typically done through:
- Static Analysis: This involves analyzing the application’s code to understand its behavior when running. The tools used here can scan the entire code in one go.
- Dynamic Analysis: This approach looks at the application’s code while it is running, providing a real-time view of its performance.
- Gaining Access: In this stage, the tester uses web application attacks like cross-site scripting (XSS), SQL injection, and indirect access attempts to uncover vulnerabilities. Once identified, they try to exploit these vulnerabilities by escalating privileges, stealing data, intercepting traffic, and so on, to understand the potential damage they could cause.
- Maintaining Access: The goal here is to determine if the vulnerability can be exploited to gain a persistent presence in the compromised system. This stage simulates advanced, persistent threats that remain in a network for extended periods, stealing sensitive information over time.
- Analysis: After the penetration test, the results are compiled into a report detailing:
- Specific vulnerabilities that can be exploited.
- Sensitive data that can be accessed.
- How long the tester was able to remain undetected in the system.
This information is reviewed by security teams to adjust WAF settings and strengthen application security measures against future attacks.
Penetration Testing Methods
- External Testing: This tests an organization’s publicly visible resources, such as web applications, websites, and email or domain name servers (DNS). The aim is to gain access and extract valuable data.
- Internal Testing: In this type of test, a tester with access to the internal network simulates an attack by a malicious insider. This scenario could be something like an employee whose credentials were stolen via phishing.
- Blind Testing: The tester is only given the name of the organization being targeted. This method provides a real-world look at how an actual attack would unfold, helping security teams respond accordingly.
- Double-blind Testing: In this case, the security team has no prior knowledge of the simulated attack, much like a real-world situation where there’s no opportunity to prepare or defend before an attack occurs.
- Targeted Testing: Here, the tester and the security staff work together and keep each other updated on progress. This is a valuable training exercise, giving security teams feedback from a hacker’s perspective.
Penetration Testing and Web Application Firewalls (WAFs)
Penetration testing and WAFs are complementary security strategies that work together to enhance overall protection.
In most types of penetration tests (except for blind and double-blind testing), testers often use WAF data, such as logs, to identify vulnerabilities in an application. After a test, the insights gained can be used to adjust WAF configurations to guard against the vulnerabilities found.
Pen testing also helps meet certain compliance requirements, such as PCI DSS and SOC 2, where standards like PCI-DSS 6.6 can only be met using a verified WAF. However, this does not diminish the importance of penetration testing, as it still provides valuable insights to improve security measures.
How Often Should You Perform Penetration Testing?
Organizations should carry out penetration testing regularly, ideally once a year, to ensure continuous security and effective IT management. Pen tests may also be necessary whenever an organization:
- Adds new network infrastructure or applications.
- Makes significant updates or changes to existing systems.
- Expands operations to new locations.
- Applies security patches.
- Modifies end-user policies.
However, the frequency of penetration testing also depends on several factors:
- Company Size: Larger organizations with a bigger online presence are more likely to be targeted by hackers and may need more frequent testing.
- Budget: Penetration tests can be costly, so smaller organizations may not be able to afford annual tests. In such cases, tests may be conducted every two years instead.
- Compliance and Regulations: Certain industries require regular penetration testing to meet regulatory standards.
- Cloud Infrastructure: Organizations relying on cloud providers might not be permitted to test the cloud provider’s infrastructure. However, the provider may be conducting their own tests.
Penetration testing efforts should be tailored to the specific needs of the organization and its industry, including continuous improvement to ensure that vulnerabilities found in previous tests are not repeated in future ones.