In recent years, the term “hacking” has become widely known. Hacking refers to the process of finding ways to gain access to a system or network, often without authorization. The person who carries out such activities is called a hacker. Hackers are typically categorized based on their intentions:
Black Hat Hacker
A Black Hat hacker is someone who hacks with malicious intent, usually for personal gain. These hackers can cause significant damage to networks, computers, and users by deleting or altering data, stealing sensitive information (like credit card details or personal data), launching Denial-of-Service (DoS) attacks, or installing harmful software to facilitate future attacks. It’s important to be cautious around these hackers.
White Hat Hacker
White Hat hackers, or ethical hackers, hack with the goal of improving security. They often work with the permission of the system’s owner, identifying vulnerabilities and suggesting fixes to strengthen the system’s defenses. Their work helps protect against malicious hackers.
Grey Hat Hacker
Grey Hat hackers share skills with both Black and White Hat hackers but act without authorization. They typically don’t have harmful intentions. Once they find vulnerabilities, they might contact the system owner and ask for a reward in exchange for sharing their findings.
Hacktivist
A hacktivist is an activist who uses hacking to promote political or social causes. Unlike other hackers, hacktivists often work in groups, which can make their attacks harder to defend against.
Script Kiddies
Script Kiddies are less skilled hackers who use pre-made tools or software to carry out attacks. Their hacking attempts are often less damaging, and they typically do it for fun or to gain fame among their peers.
How Can a Network Be Hacked?
Hacking methods have evolved over time, but the main objective remains the same: to find and exploit vulnerabilities in a device or network. Once a hacker gains access, they can infiltrate other devices connected to the network, steal, modify, or erase data, install backdoors for future access, or disable the network entirely. Here are some common hacking techniques:
Known Vulnerabilities
Hackers often take advantage of known vulnerabilities in systems or software. These vulnerabilities, like weak passwords or outdated software, can be easily exploited to gain unauthorized access.
Brute Force Attacks
In a brute force attack, hackers attempt to gain access by systematically guessing passwords. With modern technology, these attacks have become more sophisticated, often using automated tools to guess passwords more quickly.
Social Engineering
Social engineering attacks target users directly. Hackers deceive individuals into divulging personal information or granting access by posing as trusted sources. These attacks exploit the fact that people are often less cautious than security systems.
Malvertising
In this technique, hackers compromise legitimate advertisements on websites. When users click on these ads, malware is installed on their devices. This malware can redirect the user to harmful sites and infect their systems.
How to Prevent Hacking
As hackers constantly develop new methods to break into systems, it’s crucial to stay proactive in securing devices and networks. Here are some practical steps to help improve security:
1. Choose Reputable Security Software
Start by using reliable antivirus software and browsers from trusted brands. These companies have dedicated security teams that continually work to improve protection against cyber threats.
2. Purchase Software from Trusted Sources
Always acquire security products from reputable sources to avoid counterfeit versions that could be exploited by hackers.
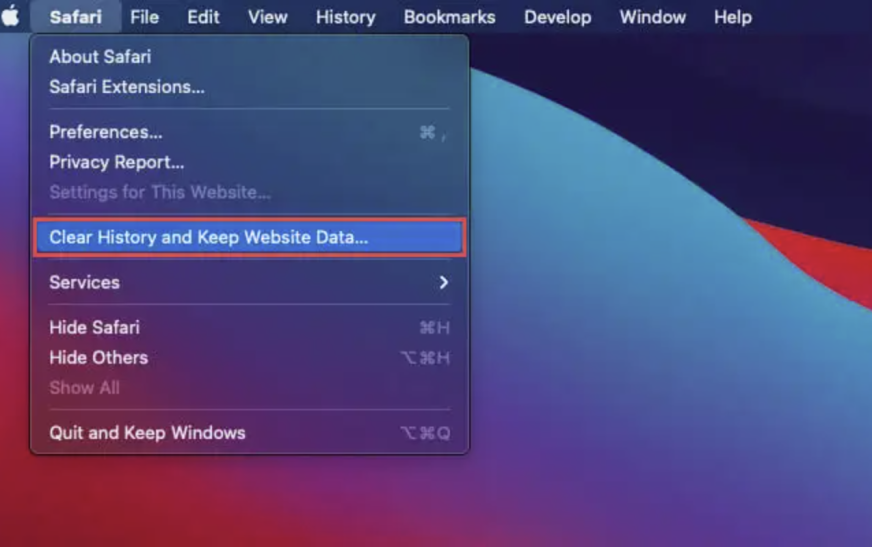
3. Regularly Update Software
Make it a habit to update your security software, browsers, operating systems, and applications. Regular updates patch security holes and provide better protection over time. Neglecting updates increases the risk of successful attacks.
4. Use Strong and Unique Passwords
Create strong passwords for each account, and avoid reusing the same password across multiple accounts. If one account is compromised, others with the same password are at risk.
5. Back Up Your Data
Regularly back up important data and store it in a secure location. This ensures that even if a hacker alters or deletes data, you’ll still have access to it.
6. Practice Safe Online Behavior
Be cautious when clicking on links or opening emails from unknown sources. Educating yourself on the latest cybersecurity threats and consulting experts when needed can also help you stay ahead of potential risks.
In conclusion, hackers will continue to search for new ways to infiltrate systems, but security measures are always improving to counter these threats. By following the above steps, users can make small but impactful contributions to their own safety and protect their systems from cyberattacks.