Understanding Encrypting Viruses
Introduction
As technology advances, so do the threats posed by cybercriminals, and one of the most dangerous is encrypting viruses. These types of malware are designed to lock or encrypt your files, making them inaccessible without the right decryption key. This article will dive into how these viruses work, the encryption methods they use, and what you can do to protect yourself.
How Encrypting Viruses Work
Encrypted ransomware is a particularly tricky type of malware. Once it infects your computer, it locks your personal files with a malicious code, making them impossible to access without decryption. This ransomware typically uses advanced encryption methods, which makes it incredibly difficult to crack or remove. The virus often spreads through unauthorized links or downloads from untrustworthy websites.
Once the virus is active, it encrypts the files on your computer, potentially stealing sensitive information in the process. The malicious software usually demands payment for the decryption key, though paying the ransom doesn’t guarantee that you’ll regain access to your files.
Encryption Methods
The encryption function behind these viruses is relatively simple in theory but incredibly complex in practice. Encryption works by converting original data into an unreadable format, using cryptographic algorithms and encryption keys. These systems ensure that unauthorized users cannot easily access or decipher the data without the proper keys.
In the case of ransomware, the encrypted files are often accompanied by instructions on how to pay for the decryption key. These files use checksum and decryption methods to protect data, and some of the more sophisticated viruses use a variety of encryption standards to make it harder to decrypt the files.
Problems Caused by Encrypting Viruses
One of the biggest challenges with encrypting viruses is that they prevent antivirus programs from detecting or removing the malware, especially once it’s already embedded within the system. The encryption process effectively shields the virus from traditional antivirus detection systems. Antivirus software may struggle to remove the malware or prevent its spread if it is not updated or designed to handle the latest encryption techniques.
Types of Encryption Algorithms
There are two main types of encryption algorithms: symmetric and asymmetric. Symmetric encryption uses the same key for both encryption and decryption, while asymmetric encryption relies on two different keys: a public key and a private key. Ransomware often uses public-key encryption, which makes it harder to crack since it requires the private key for decryption.
Ransomware and Its Effects
Ransomware is often distributed with executable files, which are used to encrypt your data. These files are protected by encryption algorithms and are typically accompanied by passwords and randomly generated numbers. Hackers use brute force attacks to try to break these encryptions, but this process can take a lot of time and effort.
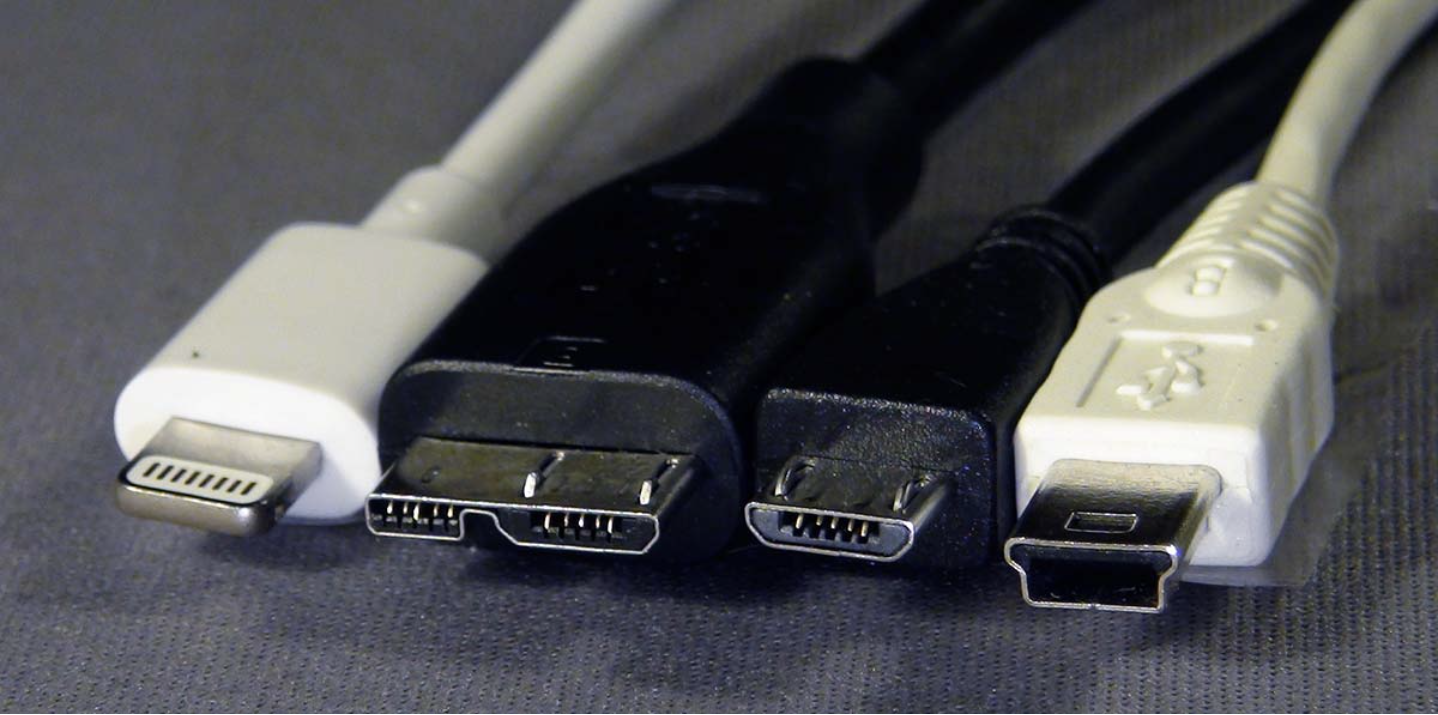
With the rise of smartphone and Android ransomware, cybercriminals are expanding their reach, making it even more important to be aware of the risks. Many antivirus scanning applications are now capable of detecting basic encrypting viruses, but they may struggle with more advanced variants, such as polymorphic or metamorphic viruses.
Polymorphic and Metamorphic Viruses
Polymorphic viruses are designed to alter their code every time they infect a new system, making them difficult to detect by traditional antivirus tools. One well-known example of this is the Dark Avenger mutation engine, which allows a virus to change its form and avoid detection. Metamorphic viruses take this a step further, constantly modifying their code during execution. These types of viruses can evade detection by even the most advanced security systems.
Preventing Encrypting Viruses
To protect yourself from encrypting viruses, consider these prevention methods:
- Back up important files regularly: Store your files in secure backups to prevent data loss in case of a virus infection.
- Be cautious with emails and SMS messages: Avoid clicking on suspicious links or opening attachments from unknown senders.
- Use reliable antivirus software: Keep your antivirus updated to ensure it can detect the latest threats.
- Don’t disable firewalls: Ensure your firewall is active to block unauthorized access to your system.
- Use a trustworthy VPN: A VPN can help protect your internet traffic and prevent hackers from gaining access to your data.
Conclusion
Encrypting viruses use sophisticated encryption methods to hide their presence and make it difficult to remove them. These viruses can scramble your program code and lock your files, demanding a ransom for their release. While encryption is designed to protect data, it can also be used maliciously to hold your information hostage. By staying informed and following best security practices, you can reduce the risk of falling victim to these types of cyberattacks.