The Boot Sector Virus (BSV) is a type of malicious software that hides in the boot sector of a disk, the area responsible for starting up a computer’s operating system. Every time a disk is mounted, the system tries to read and execute the boot sector. If the disk contains a virus in that sector, it runs automatically alongside other programs when the computer is started, spreading throughout the system. The virus replicates itself, much like a biological virus, and continues to infect other drives connected to the computer, expanding its reach.
To understand where exactly this virus hides, it’s important to know about the boot sector. It is the first sector on a disk, and its layout is determined by the operating system. Along with other files, the boot sector contains critical information about disk partitions. It is also where the virus resides. Each time the disk is mounted, the boot sector is accessed, making it the perfect place for a virus to hide and execute.
What is the Boot Sector Virus Capable of?
The main feature of the BSV is its ability to move and spread from one computer to another. This ability to transfer itself between systems distinguishes it from other types of viruses. Some other capabilities of BSV include:
- It can install itself on a computer without any permission from the user.
- It can manipulate or alter the behavior of other executable files.
- It can block access to specific system resources.
- The virus will execute whenever the parent executable file is run, even if the file appears normal.
How the Boot Sector Virus Works
When a computer is turned on, an executable file stored in the computer’s Read-Only Memory (ROM) is loaded. Since ROM is non-volatile memory, the file remains intact even when the computer is powered off. This file, called the bootstrap loader, is the first thing to run when the computer starts, initiating the operating system.
The bootstrap loader follows a predefined process to locate and execute files on the disk. Since there are often multiple executable files, it uses a jump instruction to reach the boot sector, where it finds the Master Boot Record (MBR). The MBR holds information about the disk’s partitions and allows the user to choose which partition to boot from. This area is where the virus hides, because the boot sector is one of the first to be executed, making it the ideal location for the virus to remain undetected.
The virus could be written into the disk during its manufacturing, in a place that isn’t easily scanned by antivirus programs. This hidden location is often an extra track at the edge of the disk or between the existing tracks, making it hard for security tools to detect and remove it.
The Impact of Boot Sector Virus on Windows
Once the BSV infects the Master Boot Record (MBR), it takes control of the system’s startup process. It can delete or modify files within the MBR, expanding the virus’s reach and potentially crashing the entire system. The virus spreads by corrupting the MBR, preventing the system from booting normally. In many cases, the only way to remove the virus is by completely formatting the hard drive, which leads to data loss.
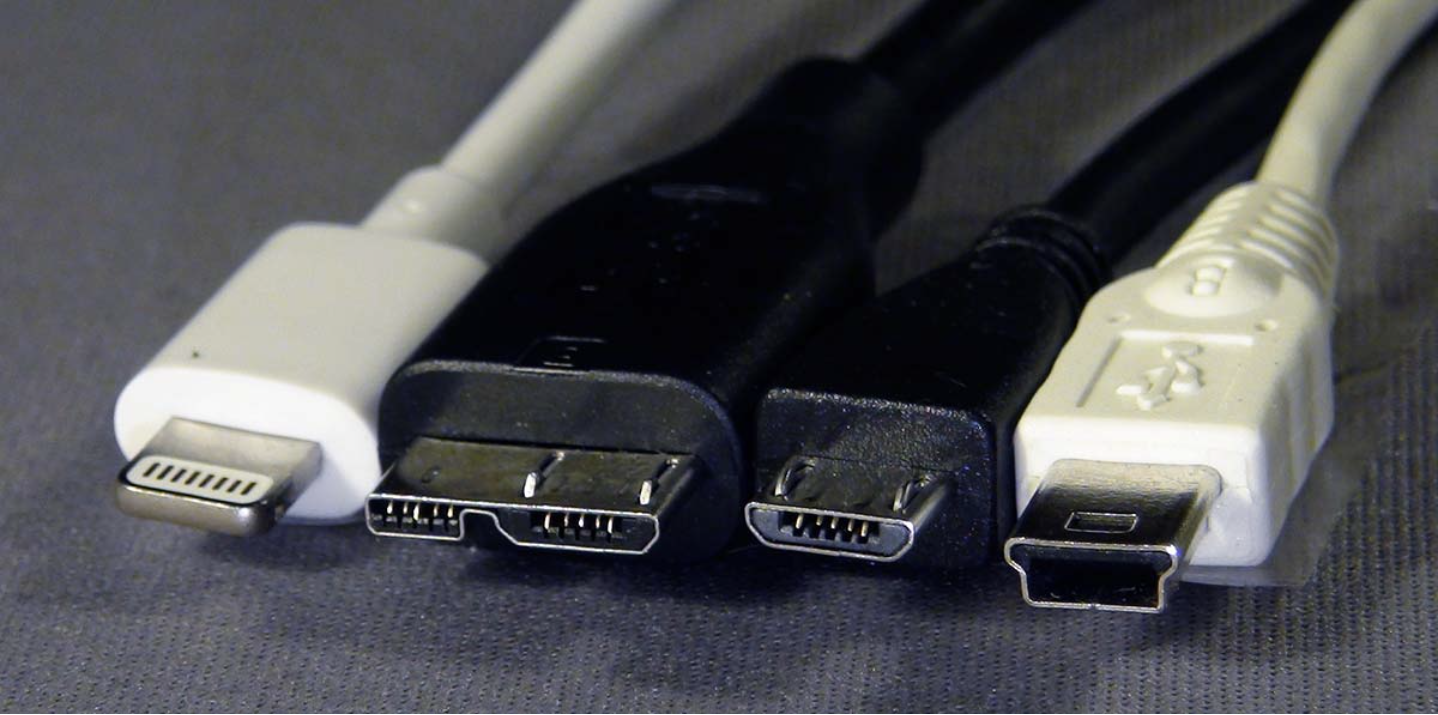
To summarize, a Boot Sector Virus infects the boot sector of a disk, where it can alter or delete executable programs. It remains in memory and is capable of moving from one device to another. If a USB or other data storage device is used, the virus can transfer itself to that device by hiding in the edges or between tracks on the disk, making it easy to spread to other computers.
Detecting a Boot Sector Virus is tricky, but one way to spot it is by noticing changes to a file’s content or properties. Typically, files won’t change unless the user intentionally updates them. If you notice any irregularities, check the file properties to see if changes were made without your knowledge. Modern antivirus software can alert you if a file has been modified unexpectedly.