Review of the SAMSUNG 27″ Essential S3 (S36GD) Series FHD 1800R Curved Computer Monitor
In today’s digital world, having a reliable and high-quality monitor is essential for both work and entertainment. The SAMSUNG 27″ Essential S3 (S36GD) Series FHD 1800R Curved Computer Monitor promises to deliver impressive specs and a curved design to meet these needs. At Online Computer Tips, we’ve examined this monitor
Steps to Take Immediately After a Hacking Incident
Immediate Actions After a Hacking Incident Introduction When your account is hacked, it’s essential to act quickly to secure your data and prevent further damage. Many of us have social media accounts linked to a single email address, and if that email is compromised, hackers can gain access to personal
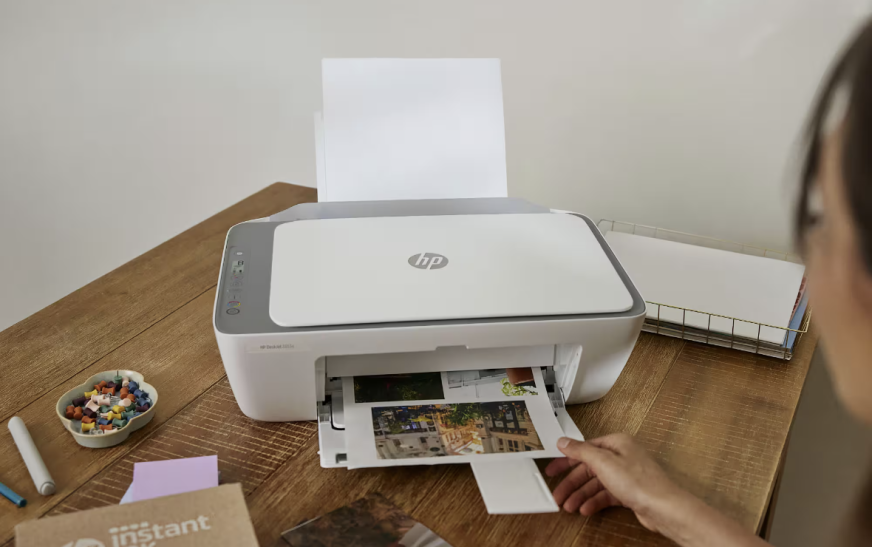
HP DeskJet 2855e Wireless All-in-One Color Inkjet Printer Review
Having a reliable and versatile printer is essential for home or small office use, and the HP DeskJet 2855e Wireless All-in-One Color Inkjet Printer aims to provide that with its multifunctional features and wireless capabilities. We’ve taken a closer look at this printer to see if it lives up to
Staying Safe When Downloading Files
Cybersecurity While Downloading Files When downloading files from the internet, it’s essential to keep cybersecurity in mind. There are many risks associated with files available online, as they may contain harmful software that can damage your device or steal personal information. To stay safe, it’s important to follow some key
Common Windows 11 Issues and How to Resolve Them
Windows is one of the most popular operating systems worldwide, developed by Microsoft, a leader in the tech industry. Over the years, Windows has dominated the OS market, consistently challenging other systems. In its early days, Windows was command-line-based, making it difficult for users. However, it later introduced the graphical
8 Essential Items Every PC Gamer Should Have
Not everyone has the luxury of dedicating an entire room just for gaming, but some people do need a well-equipped gaming setup to support their work or passion. If you’re fortunate enough to have a dedicated space for gaming, there’s always room to make it even better. Here’s a list
WHITE HAT AND BLACK HAT HACKERS
In this blog, I want to talk about white hat and black hat hackers, specifically how they operate and their impact on cybersecurity. Introduction Hacking techniques can steal sensitive information, and security measures are constantly evolving to protect networks from cybercriminals. The world of cybersecurity includes both legal and illegal
4 Methods to Recover Data from a Failing External Hard Drive
External hard drives are essential for transferring and storing data, allowing us to carry several terabytes of information wherever we go. As a result, many people rely on them for backups and data management. However, these devices are fragile and can easily be damaged, leading to the potential loss of
Emerging Cybersecurity Trends in IT Services: Safeguarding Your Business in 2025
As technology continues to evolve, businesses must adapt to stay competitive by digitizing their operations. Companies that succeed focus on enhancing their online presence, automating processes, and leveraging technological advancements. However, with the increase in technology use comes the need for heightened attention to cybersecurity. By 2025, cybersecurity threats are
Everything You Need to Know About AI-Fuzzing
What is AI Fuzzing? AI fuzzing is an important technique used to identify vulnerabilities in systems or networks. Fuzzing is an automated testing method that involves sending random or invalid data to a system to see how it behaves and identify potential weaknesses. Fuzzing has been around for a while,